by Jim Jessup | Feb 9, 2026 | eBooks
The Buyer’s Guide to Privileged Access & Identity Security Most security demos are built to impress, not to work in real environments. This guide helps you evaluate privileged access and identity security tools based on real risk, real workflows, and the questions...
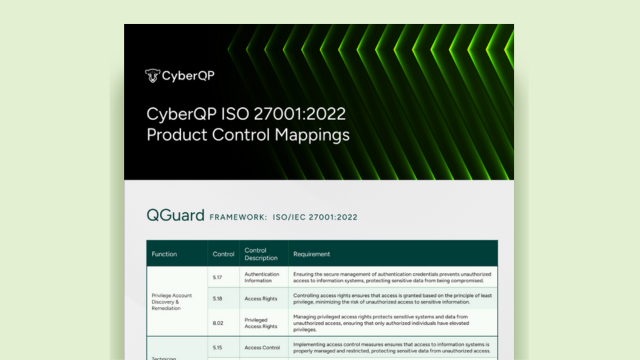
by Jim Jessup | Jan 29, 2026 | eBooks
EBOOK ISO/IEC 27001:2022 CONTROL MAPPINGS Access the Guide Home Page 2 Search results for: Just in Time Download the ISO/IEC 27001:2022 Mappings and Prove Your Access Controls See How CyberQP Aligns Meeting ISO/IEC 27001 requirements around access control,...
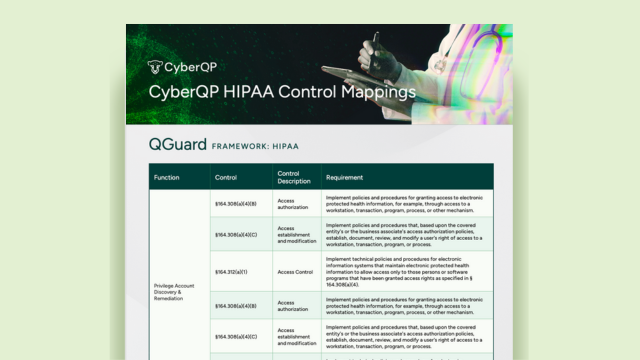
by Jim Jessup | Dec 31, 2025 | eBooks
EBOOK HIPAA CONTROL MAPPINGS Access the Guide Home Page 3 Search results for: Identity Verification Download the HIPAA Control Mapping and Prove Your Access Controls Where Access Is Granted, Security Must Be Enforced. Healthcare breaches don’t start with networks,...
by Jim Jessup | Dec 19, 2025 | Articles
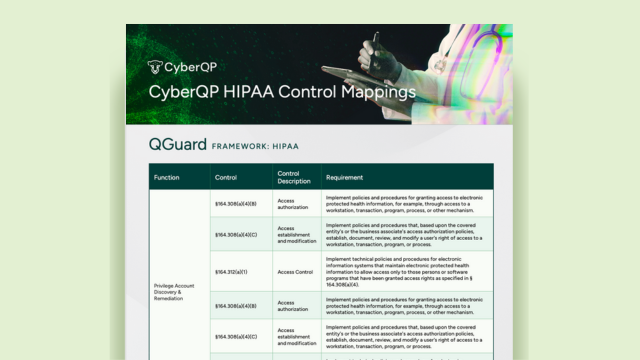
Stop Privileged Sprawl Before It Spreads You can’t protect what you can’t see. Discover, audit, and remediate every privileged account before attackers find them. Home Search results for: Just+in+Time New Feature: Local Admin & UAC Remediation Privileged Access...

by Jim Jessup | Nov 13, 2025 | Blog Posts
The Louvre Heist that Turned into a Password Horror Story When investigators revealed that the password to the Louvre Museum video surveillance system was simply “Louvre”, it sounded like a meme. It was not a joke. According to reports and a museum employee, that...