Thank You For Downloading Privileged Access Management Landscape for MSPs eBook
Click the button below to receive your download.
Here are Some Additional Resources You Might Be Interested In
Basic JIT Access Isn’t Enough (healthcare)
Basic JIT Access Isn’t Enough. Discover CyberQP’s new Customer-Scoped JIT Policies that deliver precise, granular control over privileged access. Strengthen security, simplify compliance, and see the difference in a personalized demo.
Basic JIT Access Isn’t Enough (Finance)
Basic JIT Access Isn’t Enough. Discover CyberQP’s new Customer-Scoped JIT Policies that deliver precise, granular control over privileged access. Strengthen security, simplify compliance, and see the difference in a personalized demo.
Basic JIT Access Isn’t Enough (Education)
Basic JIT Access Isn’t Enough. Discover CyberQP’s new Customer-Scoped JIT Policies that deliver precise, granular control over privileged access. Strengthen security, simplify compliance, and see the difference in a personalized demo.
CyberQP Announced as one of Deloitte’s Technology Fast 50 Program Winners for 2025
CyberQP is recognized as a 2025 Deloitte Technology Fast 50 winner, celebrating rapid growth and innovation in Zero Trust access management.
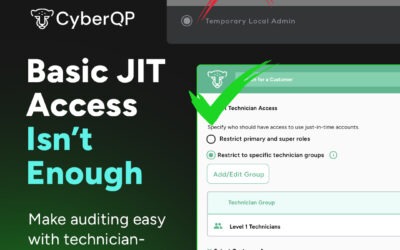
Basic JIT Access Isn’t Enough
Basic JIT Access Isn’t Enough. Discover CyberQP’s new Customer-Scoped JIT Policies that deliver precise, granular control over privileged access. Strengthen security, simplify compliance, and see the difference in a personalized demo.
5 Ways Service Desks Can Reduce Risk and Save Time
IT leaders are constantly juggling the demands...
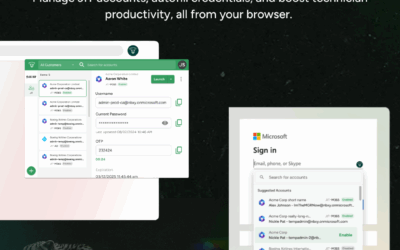
CyberQP QTech Browser Extension | JIT Account Management & Credential Autofill for Faster, Secure Privileged Access in Chrome & Edge
We’re excited to announce the release of the...
How CyberQP Helps You Stay Compliant Without the Complexity
Regulations are tightening, and auditors aren’t...
Privileged Access. Now In Your Browser.
Experience privileged access management directly in your browser with CyberQP’s QTech Chrome Extension. Eliminate copy-paste hassles, save time for your techs, and see how PAM just got easier.
Don’t Let Stolen Privileges Trigger A Second Breach
Partner with CyberQP for an all in one PAM, EUAM, and Identity Verification solution. Driven by our commitment to give IT professionals tools that help them stay ahead, we have expanded our capabilities to close the gaps attackers look for.
Consolidating with CyberQP
Partner with CyberQP for an all in one PAM, EUAM, and Identity Verification solution. Driven by our commitment to give IT professionals tools that help them stay ahead, we have expanded our capabilities to close the gaps attackers look for.
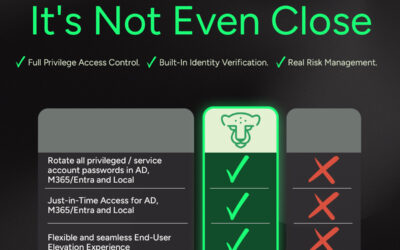
It’s Not Even Close.
Partner with CyberQP for an all in one PAM, EUAM, and Identity Verification solution. Driven by our commitment to give IT professionals tools that help them stay ahead, we have expanded our capabilities to close the gaps attackers look for.