Thank You For Downloading Privileged Access Management Landscape for MSPs eBook
Click the button below to receive your download.
Here are Some Additional Resources You Might Be Interested In
Duo for End-User Identity Verification | CyberQP Product Release
CyberQP introduces Duo Push for end-user identity verification in helpdesk workflows. Extend your existing MFA investment, reduce social engineering risk, and verify users with confidence.
20% Off Zero Trust Access Management | CyberQP Special Offer
For a limited time, receive 20% off CyberQP. If you’re looking to strengthen identity verification, control privileged access, and simplify audit or insurance conversations, this is the perfect time to get started. Book time with our team here and secure the deal.
Cyber Insurance Readiness Checklist
Secure cyber insurance without delays or denials. Learn what underwriters require, how to prove MFA and PAM controls, and how IT Teams can align with CMMC, NIST, and modern coverage standards with confidence.
Obtain Cyber Insurance Without The Hassle
Secure cyber insurance without delays or denials. Learn what underwriters require, how to prove MFA and PAM controls, and how IT Teams can align with CMMC, NIST, and modern coverage standards with confidence.
Pink Whales Foundation Masters
Join CyberQP in Greater Boston for the 3rd Annual Pink Whales Foundation Masters, a tournament for IT leaders. Enjoy 18 holes, on-course contests, a post-tournament reception, and a Masters-Style Jacket Ceremony, all supporting the Pink Whales Foundation. Limited spots available.
PAM & Identity Security Buyer’s Guide
Download the CyberQP ISO/IEC 27001:2022 Product Control Mapping to see how QGuard and QDesk align with key access, authentication, and privilege controls.
Supporting Microsoft GCC High Environments | CyberQP Product Release
CyberQP now supports Microsoft GCC High, extending full privileged access management capabilities to high-compliance government and defense environments.
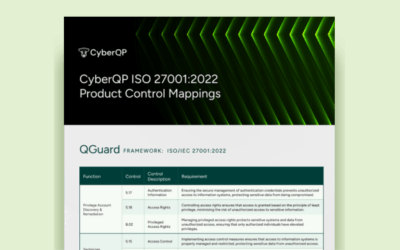
ISO 27001:2002 Product Control Mappings
Download the CyberQP ISO/IEC 27001:2022 Product Control Mapping to see how QGuard and QDesk align with key access, authentication, and privilege controls.
QTech Mobile App: End User Elevation Requests | CyberQP Product Release
End User Elevation Requests are now available in the CyberQP QTech mobile app. Review and approve requests on the go while enforcing least-privilege security.
CyberQP Looks Different
Re-discover CyberQP. See how our latest product releases improve our PAM and EUAM offerings. Explore the future of Zero Trust Access Management today.
We Appreciate Your Interest
Interested in learning more? Schedule a demo to explore the full solution and see how Zero Trust Access Management strengthens identity and privileged security for IT teams.
Trust but Verify: Stopping Identity-Based Breaches
Attackers aren’t always breaking systems. They’re logging in. Tune in to our webinar about how weak identity verification, reused or poorly managed credentials, and over-privileged accounts make it easy for hackers to impersonate users and move through organizations undetected.
In this webinar, we’ll show why traditional access models fail and how a Trust but Verify approach can protect your organization. You’ll see how identity verification and proper credential management prevent impersonation, limit privilege abuse, and reduce risk.