
Built-to-Solve Series: Protecting GCC High Environments with Built-In Privileged Access Controls
Microsoft GCC High environments are required for organizations handling regulated data, but most security and PAM tools can’t operate there. This has forced IT teams to rely on manual processes, inconsistent controls, and alternative workflows for their most compliance-sensitive customers. And we’re here to show how you can now protect and secure your GCC High customers with the power of CyberQP.
In this session of our Built-to-Solve Series, we’ll explain the benefits of GCC High when it comes to enabling Just-in-Time access, identity verification, and privileged access controls directly inside these sensitive environments. You’ll also see how this capability supports CMMC and NIST 800-171 requirements while allowing technicians to manage GCC High customers from the same dashboard and workflows they already use.
Join us to learn how to securely support defense and government customers without security gaps or tool limitations.
Presenters
A Fireside Chat: Transparency, Compliance, & Control
Security and compliance don’t have to be complicated. Join CyberQP and Hudu for a live, interview-style webinar, where product and security leaders break down how combining documentation with privileged access management can transform the way IT teams operate.
We’ll show you how to:
- Eliminate standing privileges without slowing down your techs
- Automate identity verification and access logging
- Track sensitive actions with real-time documentation
We’ll discuss how transparency builds trust, why audit readiness starts at the helpdesk, and how your team can work more efficiently without sacrificing control. If you’re managing sensitive access and documentation separately, it’s time to rethink your stack.
Presenters
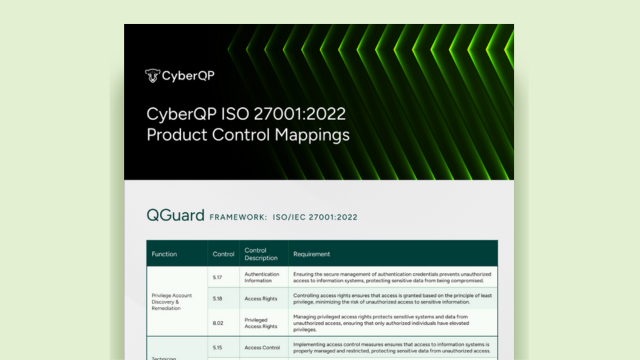
ISO 27001:2002 Product Control Mappings
EBOOK ISO/IEC 27001:2022 CONTROL MAPPINGS Access the Guide Home Page 3 Search results for: Identity Verification See How CyberQP Aligns Meeting ISO/IEC 27001 requirements around access control, authentication, and least privilege is challenging without the right...
