Duo for End-User Identity Verification | CyberQP Product Release
A Smarter Way to Verify End-User Identity
CyberQP is expanding identity-first security controls with a new identity verification option, Duo Security. This targeted release enables MSPs and IT teams to standardize on Duo Push for end-user identity validation during support interactions, extending existing MFA investments directly into helpdesk workflows.
As social engineering attacks increasingly target service desks, identity verification can no longer rely on knowledge-based questions or caller familiarity. Verification must be immediate and auditable.
Why We Built This
Verifying end-user identity is one of the most critical controls in preventing unauthorized password resets, privilege elevation, and sensitive configuration changes. CyberQP already supports multiple verification methods, however, many partners requested the ability to leverage Duo, their trusted MFA provider, as part of helpdesk validation workflows.
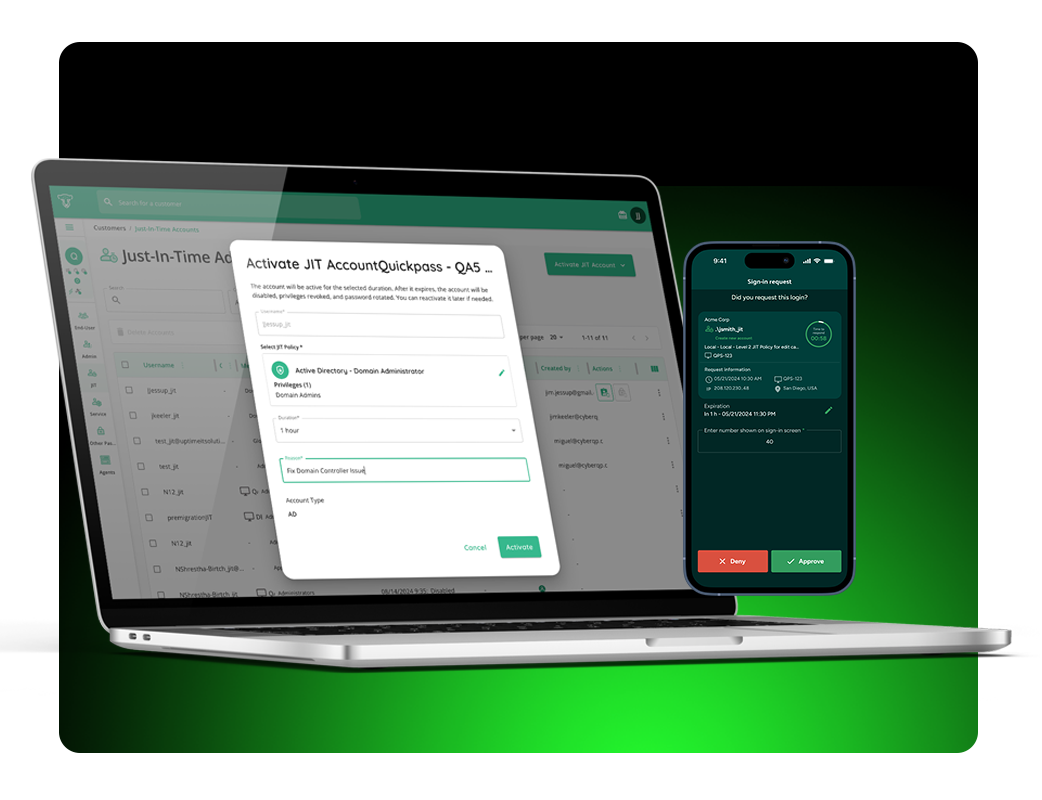
How It Works
When a technician initiates an identity verification request:
- The end user receives a Duo Push notification on their enrolled device.
- The user approves or denies the request.
- The result is immediately reflected inside CyberQP.
Technicians receive clear confirmation before proceeding with password resets, account unlocks, or privileged actions. Check out our KB article, Verify End-User Identity with DUO, for more technical information.
Key Benefits
-
Leverage Existing MFA Investments
You can use Duo for identity verification without deploying new tools or reeducating customers. -
Stronger Protection Against Social Engineering
Duo Push adds a trusted, user-approved verification step before sensitive actions are taken. -
Faster, More Confident Support Interactions
Technicians can verify identity quickly and proceed with confidence. -
Consistent Experience Across Platforms
Duo verification is already a trusted authentication method you customers are used to.
Designed for Real-World Environments
This feature was built to align with how you operate at scale:
-
Automatically associates end users with their Duo accounts
-
Provides clear guidance when users are not enrolled or setup is incomplete
-
Ensures verification events are recorded for visibility and auditing
To learn more about Duo Push identity verification, book a demo today.