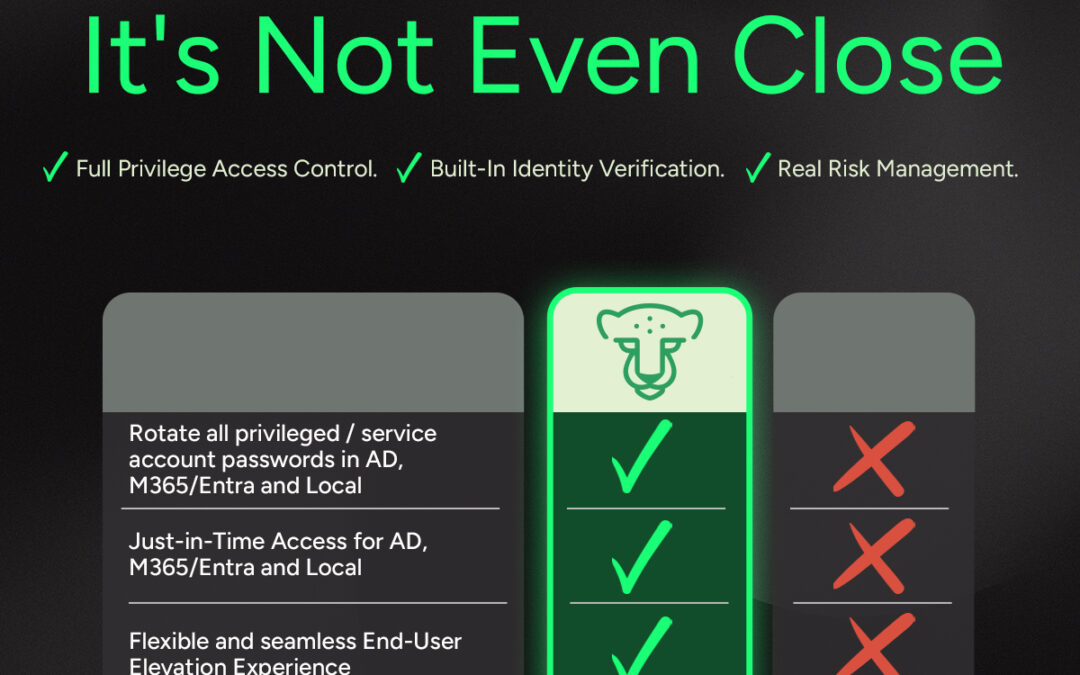
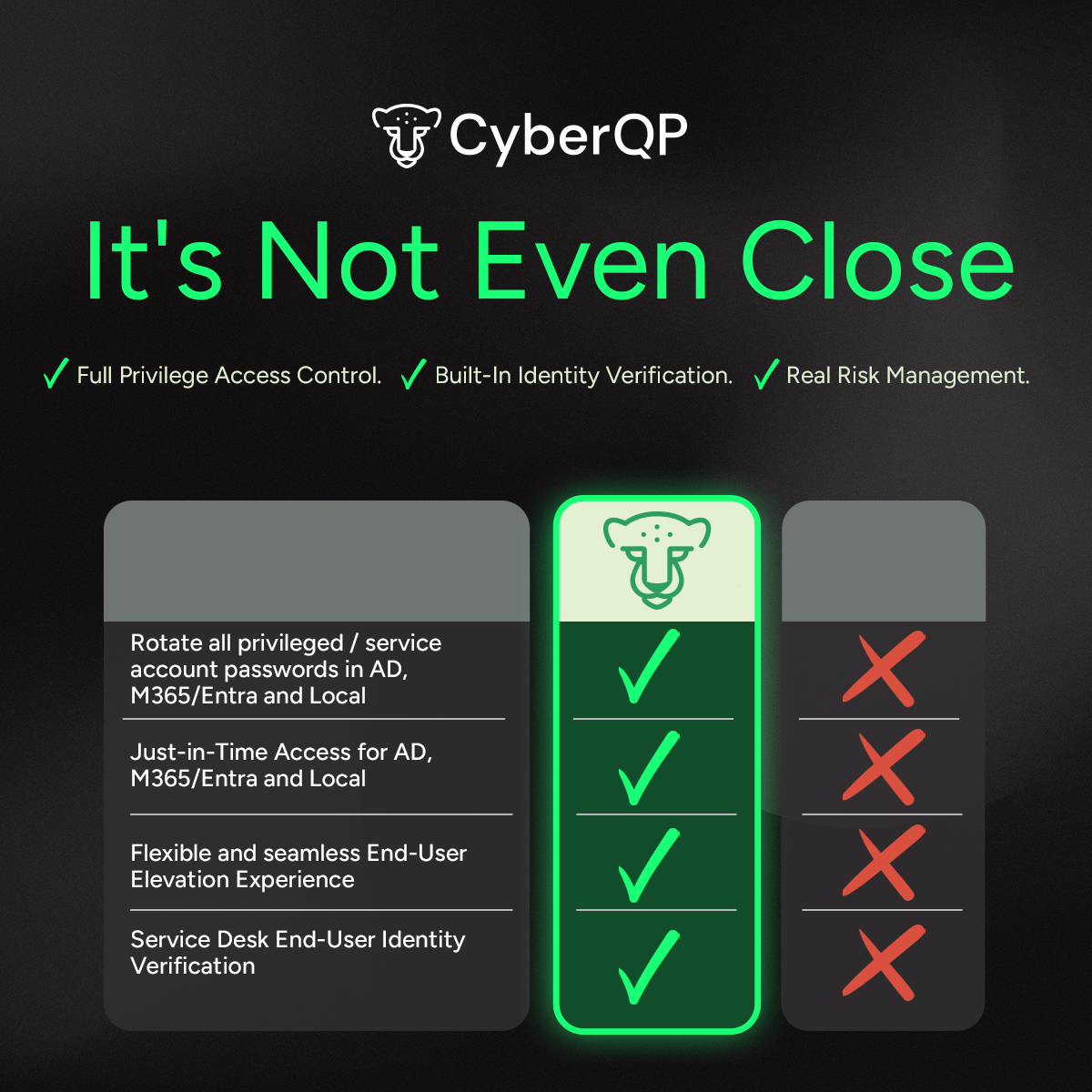
It’s Not Even Close.
All-in-One PAM + EUAM Platform Built for MSPs
One Pane, Zero Complexity.
Partner with CyberQP for an all-in-one Privileged Access Management (PAM) and End User Access Management (EUAM)
Slash password-related tickets, enforce least privilege access, and sharpen compliance – all from a single dashboard.

CyberQP brings all solutions together in one purpose-built platform, giving IT teams a faster, smarter, and more secure way to manage these critical workflows through one pane of glass. Our platform provides secure, elevated access for both IT Professionals and end-users, along with robust self-service and identity verification capabilities.
Why Access Management Matters
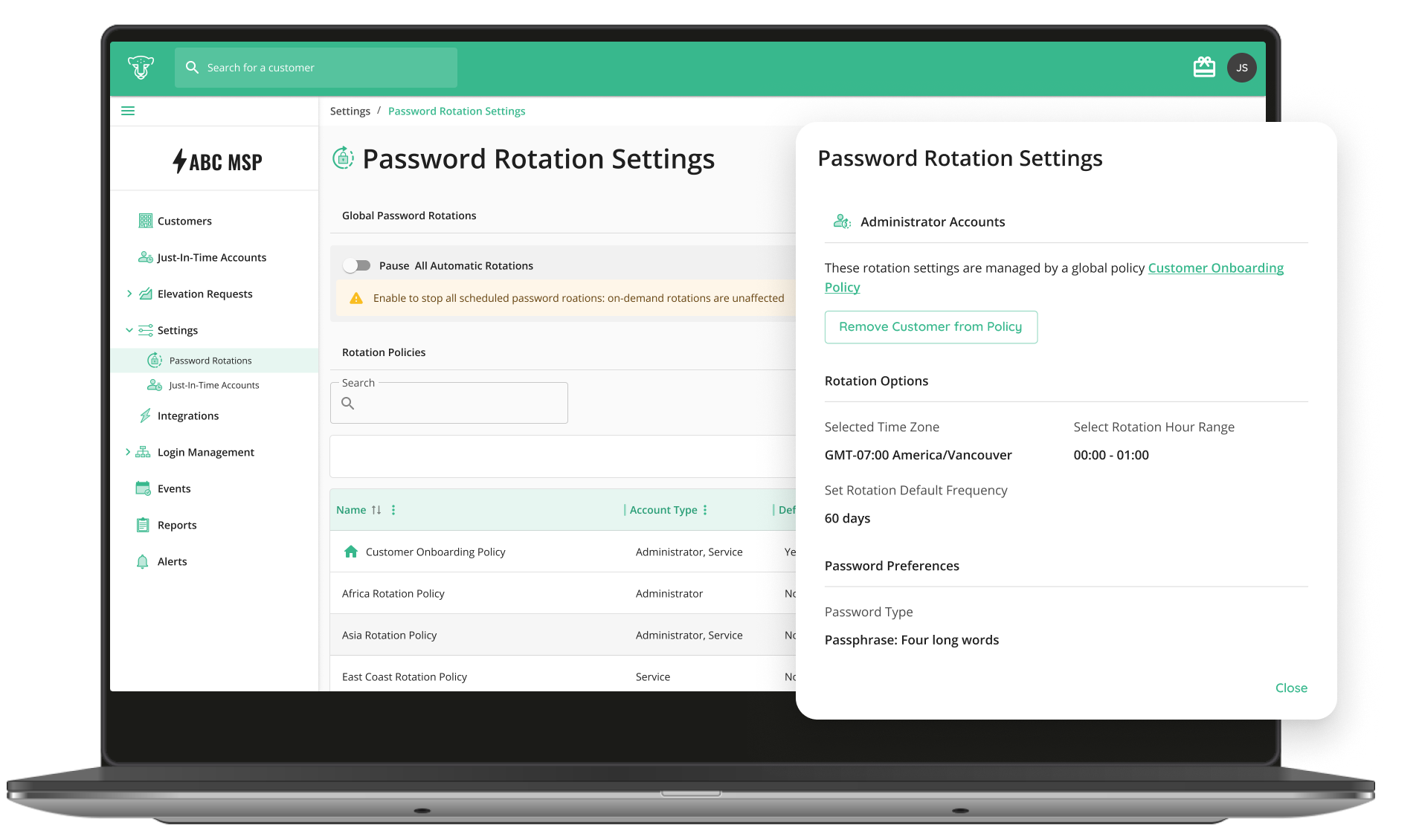
Eliminate All Static Credentials
67% of organizations admit they cannot fully determine if their privileged users are violating policies. Meet Compliance and Cyber Insurance Requirements: CyberQP includes mappings to many identity security controls to compliance frameworks such as NIST 800-53, CIS V8, CMMC 2.0, HIPPA and ISO 27001. Allowing organizations to meet both compliance and Cyber Insurance requirements.
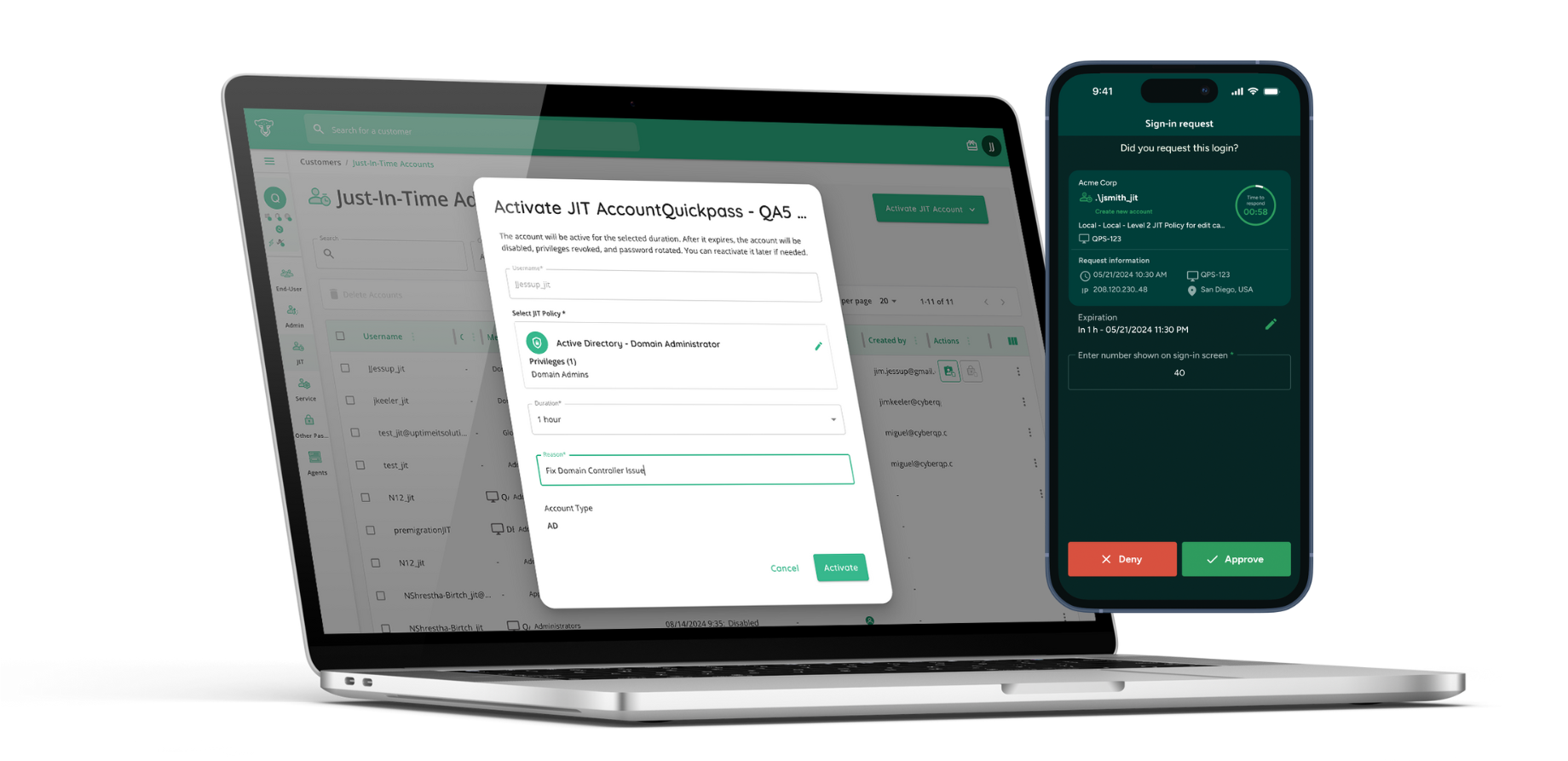
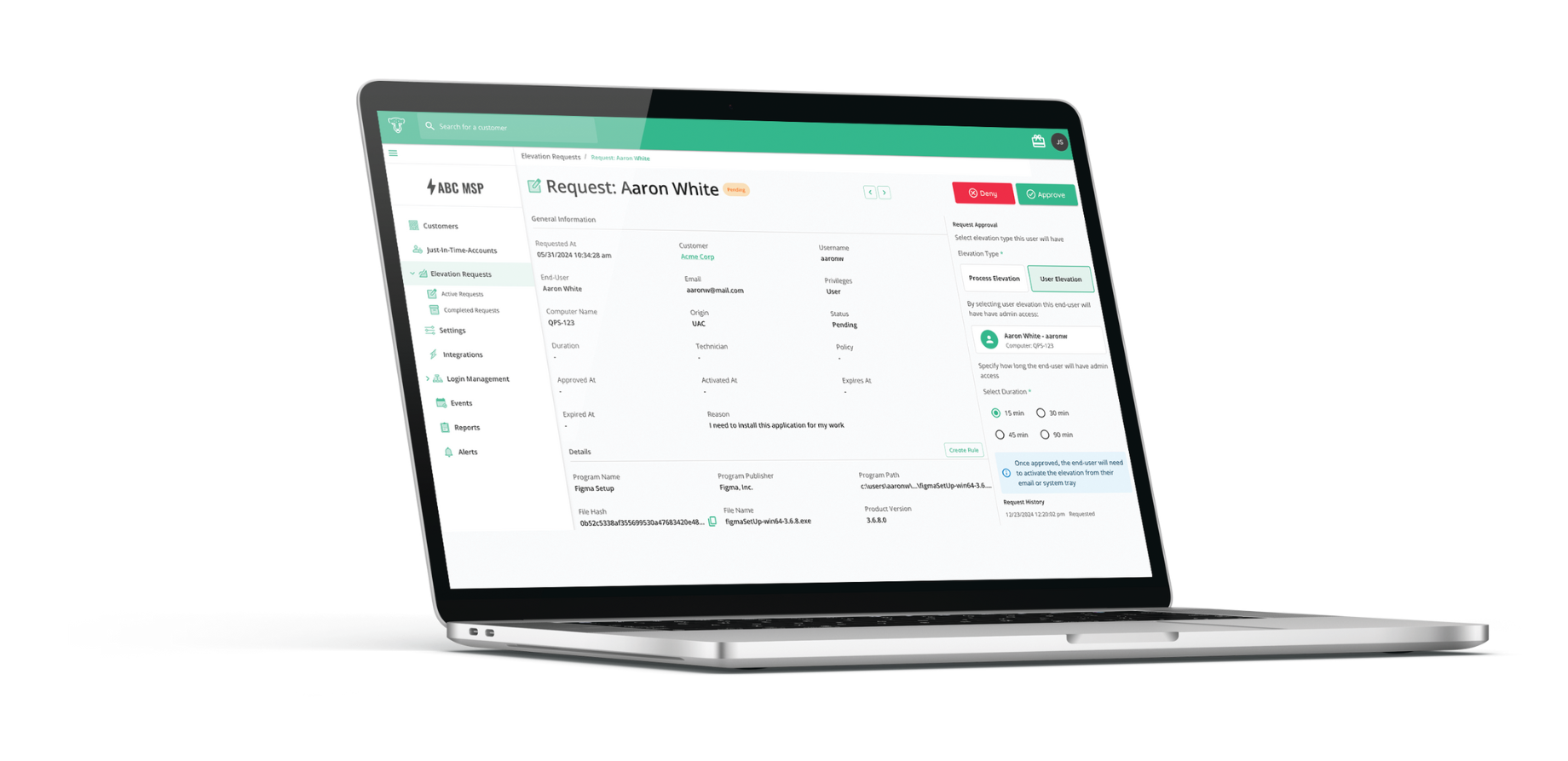
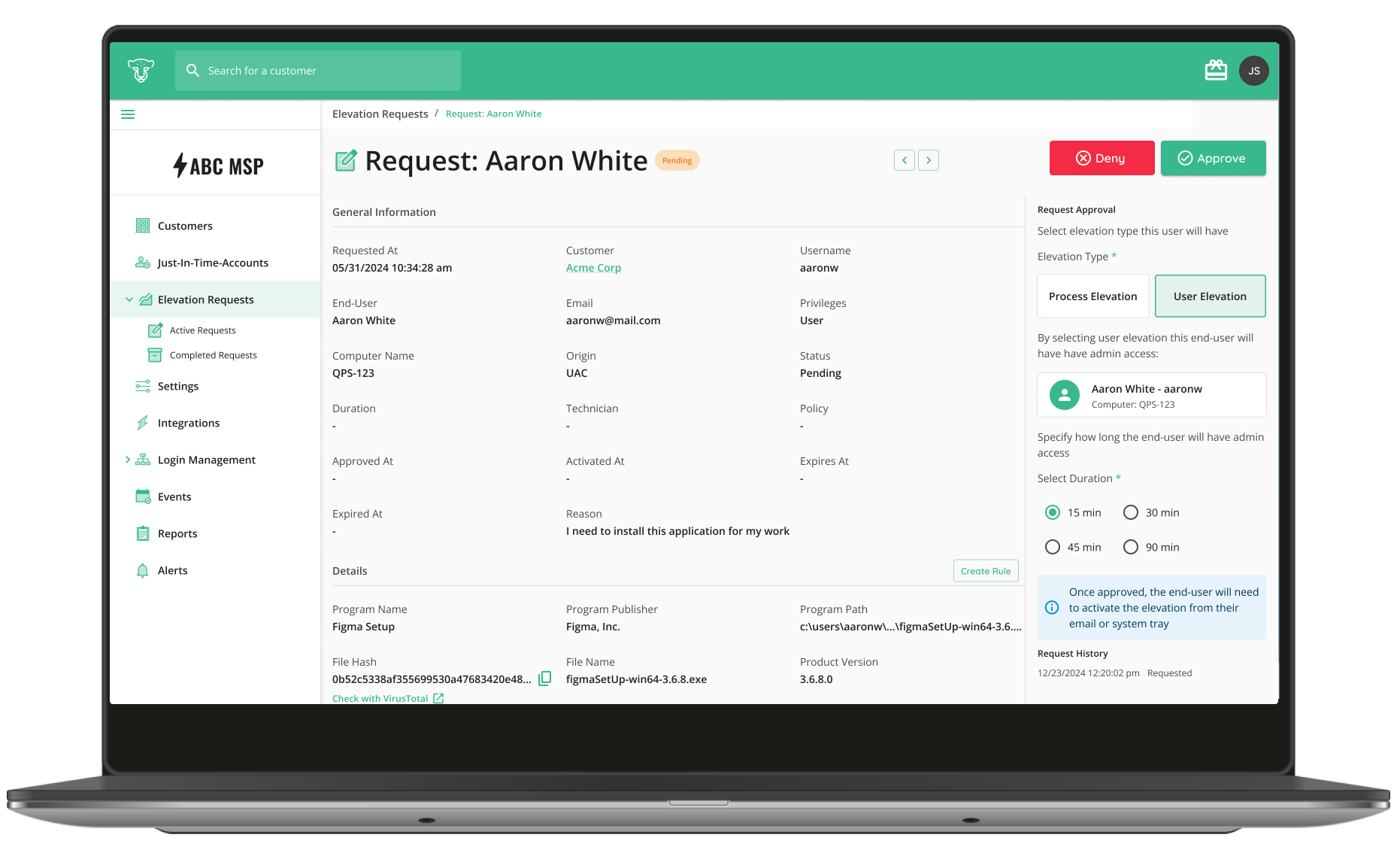
Zero Standing Privilege with Just-in-Time Access
61% of breaches involve lateral movement post-initial compromise. Achieve Zero Standing Privilege: Eliminate persistent admin rights by provisioning Just-in-Time access. Grant only the exact privileges needed, only when they’re needed, minimizing your attack surface and enforcing true least privilege.
Built-In Identity Verification for EUAM
80% of hacking-related breaches are due to stolen or compromised credentials. Prevent Social Engineering & Impersonation Attacks: Defend IT service desks against social engineering, impersonation, and insider threats that can lead to unauthorized access, data breaches, or privilege escalation. Empower service desk technicians with multiple options to verify end-user identities.
QGuard. Eliminate ALL Static Credentials
Don’t settle for ‘good enough’. Attackers are exploiting static, long-standing service and admin passwords. Rotate your privileged/service accounts in AD, M365/Entra, and Local admins through one easy-to-use dashboard automatically (daily, weekly, monthly, quarterly, or yearly).
Protect Identities. Control Privileges. Empower Users.
CyberQP’s QDesk solution offers your team a necessity that the Fox does not. End-User Access Management to provide controlled temporary admin access for your customers and seamless identity verification to prevent social engineering and impersonation attacks.
MSPs Love How Quickly We Simplify Access Management
For us, we got into CyberQP because we wanted password rotation, and we wanted the Just-in-Time (JIT) system. We wanted all of those tools, and CyberQP fit that really well for us.