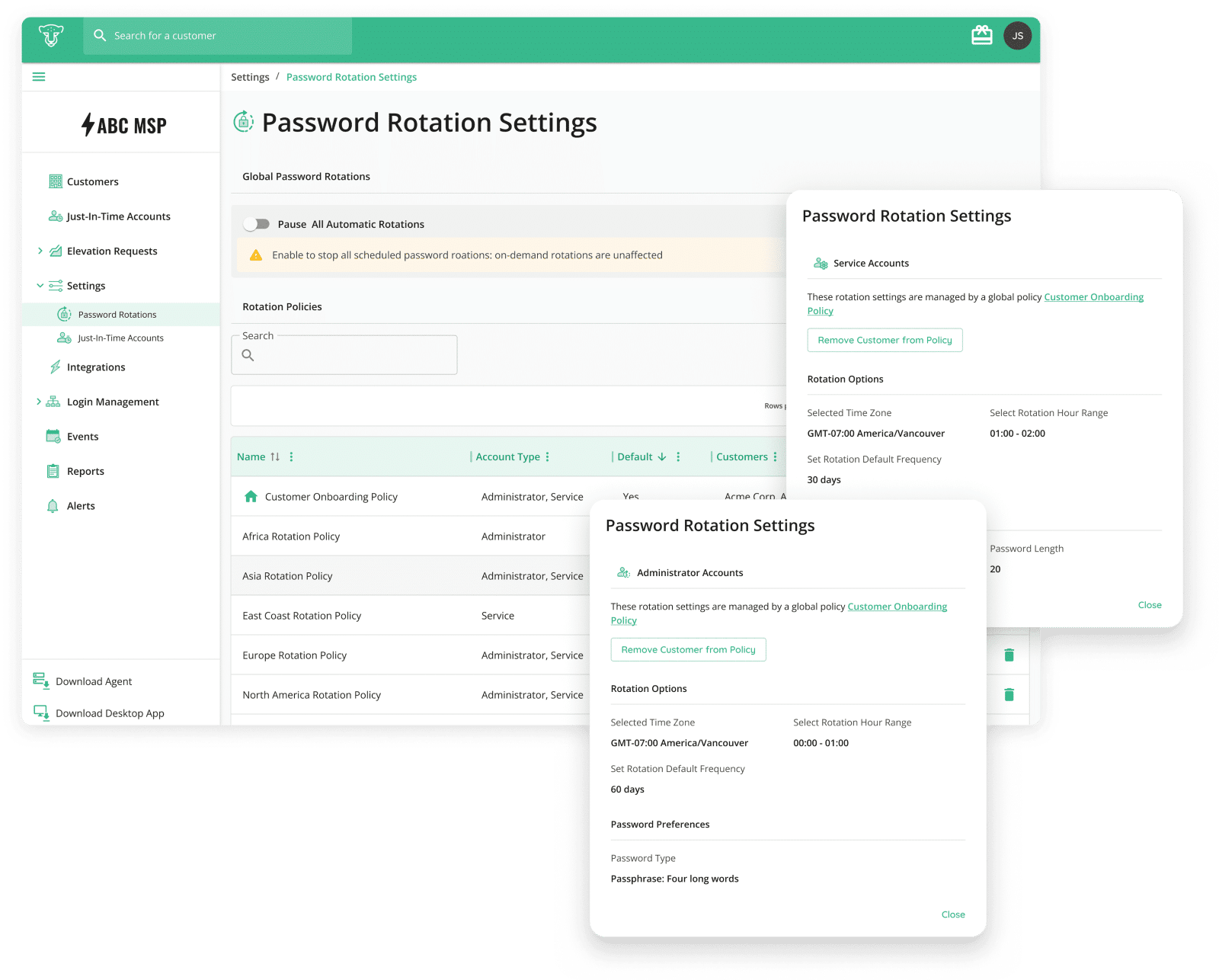
The introduction of Password Rotation Policies on CyberQP marks a significant advancement in account security and operational efficiency for MSPs. By centralizing control over password settings, we empower you to safeguard your customers’ accounts while simplifying your operational processes.
Are you ready to elevate your security practices and streamline your account management? Log into your CyberQP account today and implement Password Rotation Policies across your customer base!
For more information, reach out to our support team or visit our documentation. Together, let’s secure the future of your clients and your business.
Stay secure and happy managing!
—
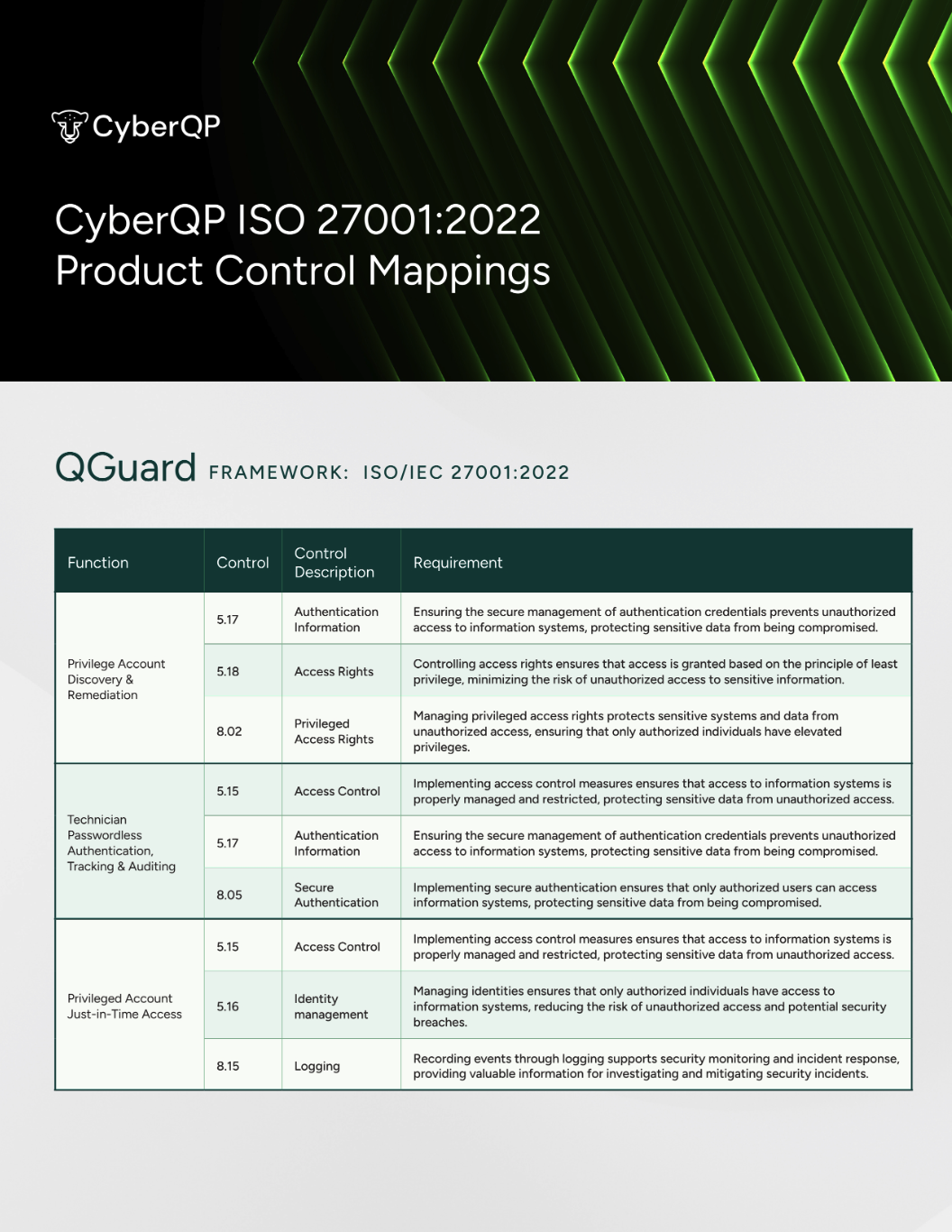
CyberQP redefines help desk security through privileged access management, help desk verification, and user privilege elevation. We empower MSPs and IT professionals to eliminate standing privilege risks, enforce compliance, and streamline operations. Committed to “Empowering Access, Redefining Privilege,” CyberQP protects accounts, credentials, and identity verification with innovative, efficient solutions. Learn more at https://cyberqp.com/tours/