Cyber Insurance Readiness Checklist
Get Ahead of Insurance Season
See How Ready You Really Are
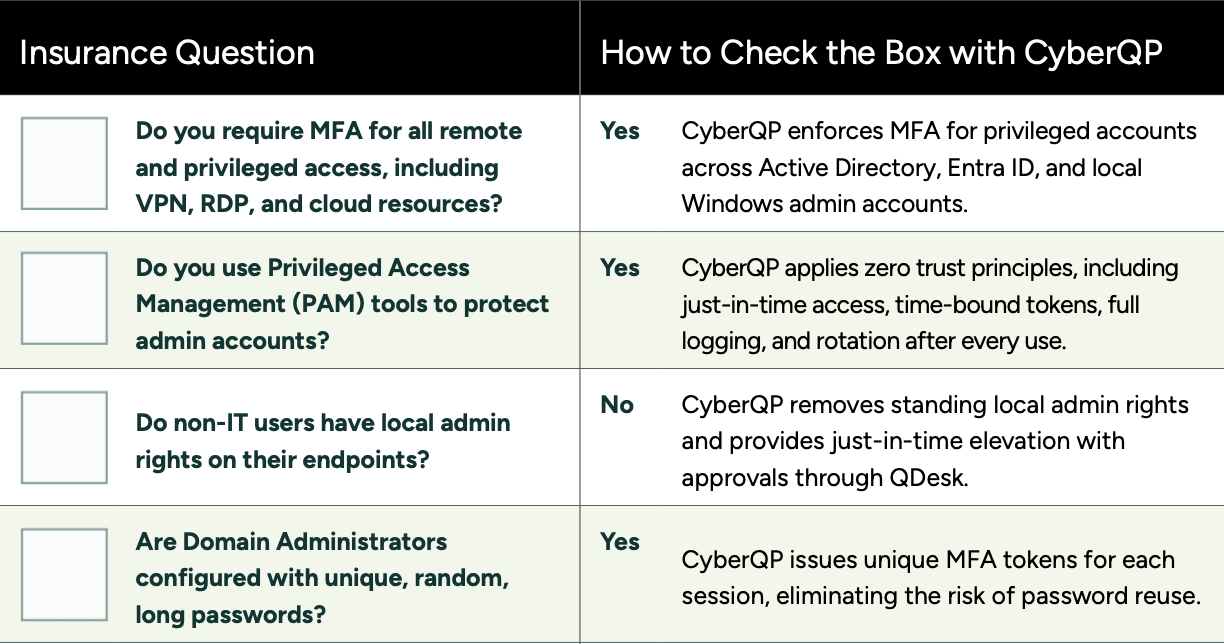
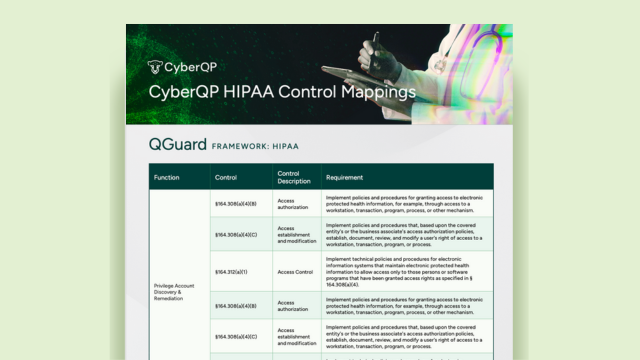
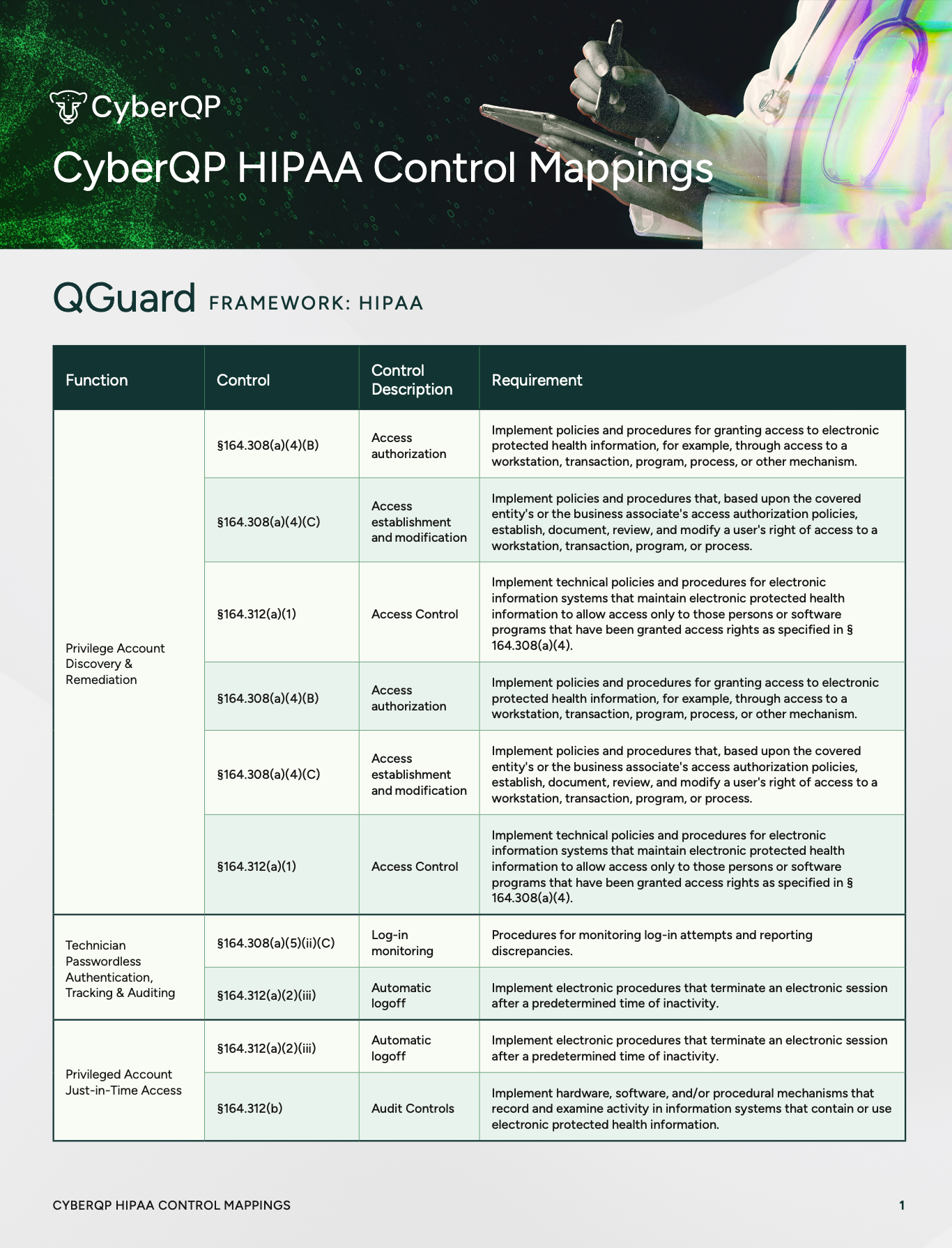
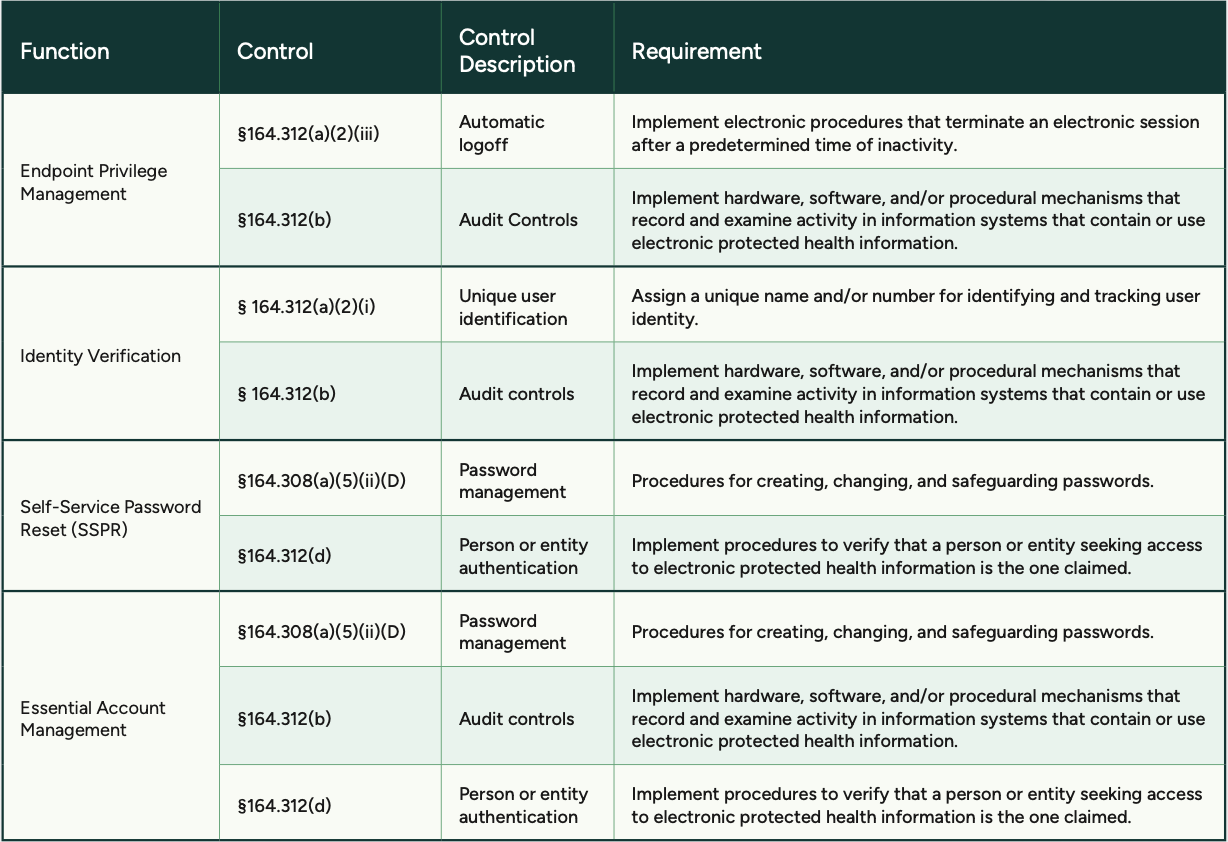
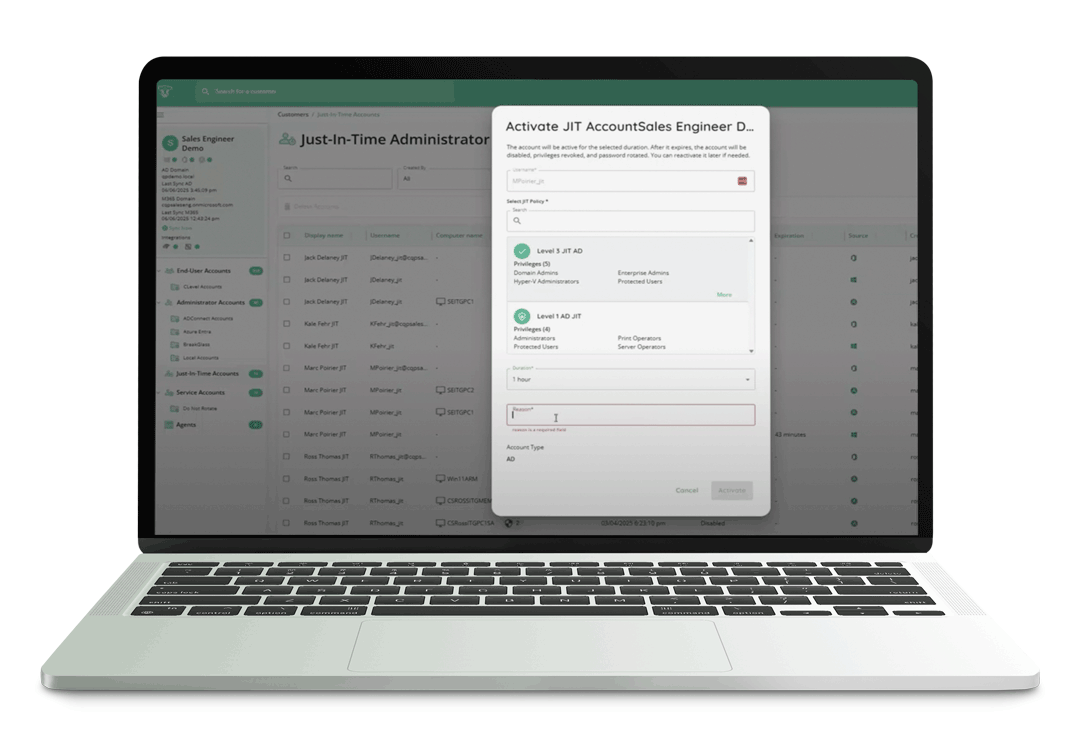
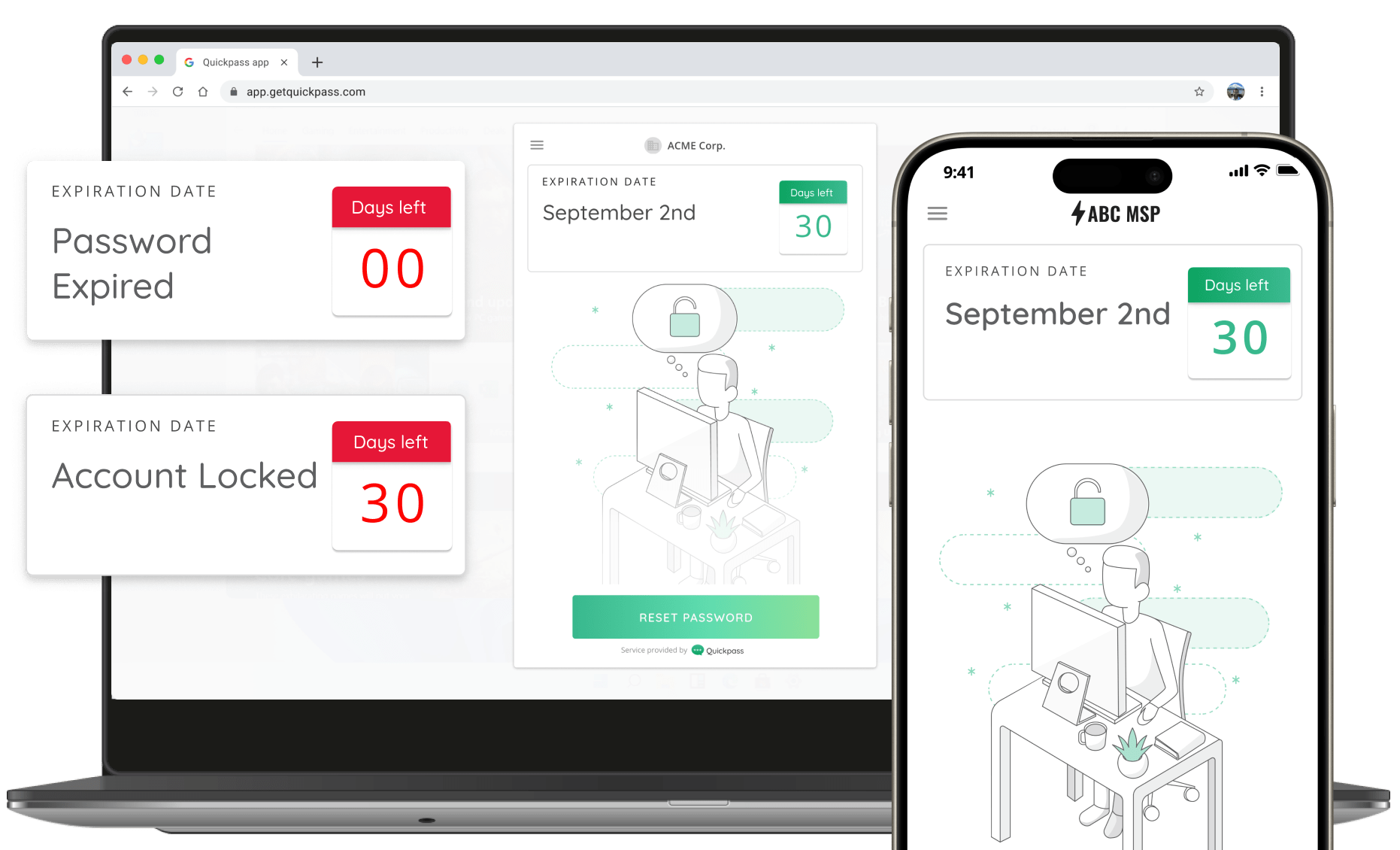
Cyber insurance applications aren’t just about answering “yes.” Underwriters want proof. Our Cyber Insurance Readiness Checklist shows exactly what you’ll be asked and how to demonstrate compliance, from MFA enforcement and privileged access controls to audit-ready evidence and deprovisioning workflows.
With this checklist, you can:
- Quickly verify your security posture before applications hit your inbox
- Ensure every answer is backed by proof, not guesswork
- Protect your coverage and avoid costly denials
Above is a sneak peek of the checklist itself, a practical tool you can print, share with your team, and start using today.
When “Yes” Isn’t Verifiable
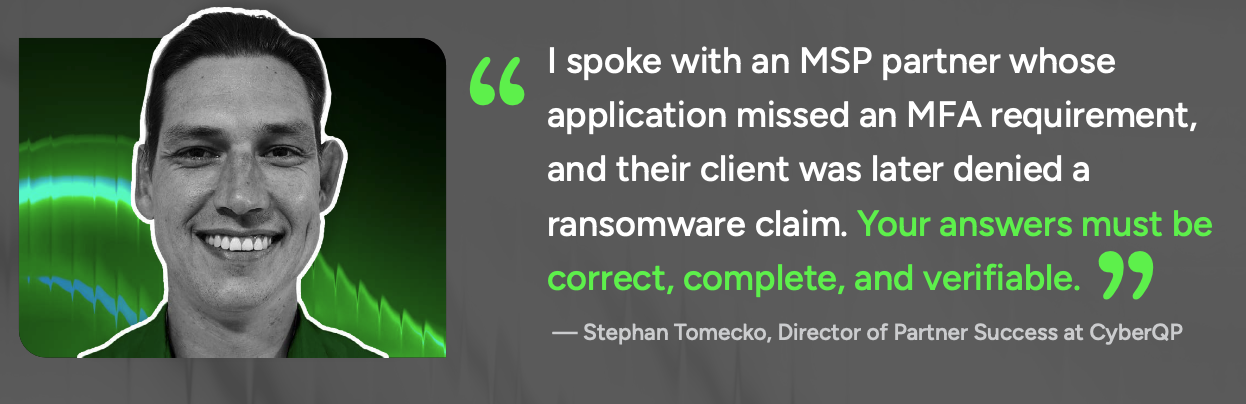
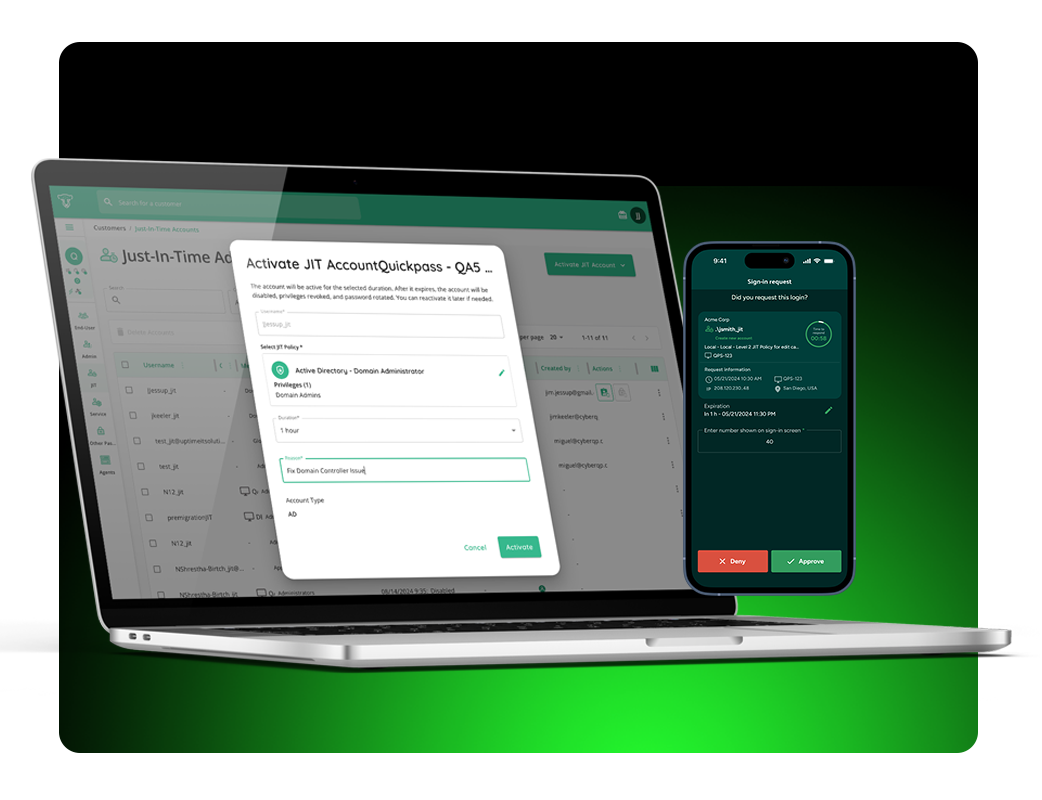
The application process doesn’t have to be so daunting. CyberQP maps identity and access controls directly to underwriting requirements, ensuring your answers are accurate, defensible, and ready when carriers or auditors request proof.
Don’t wait until it’s too late. This checklist makes it fast and easy to evaluate your environment and ensure you’re prepared for insurance season. Share it with your team, review your controls, and approach applications with confidence. Click below to download your Cyber Insurance Checklist and get ahead today.