Obtain Cyber Insurance Without The Hassle
Cyber insurance applications are no longer simple checklists, they’re risk declarations that require proof. Documented enforcement of MFA, privileged access management, identity controls, and audit logging is expected before coverage is approved. This guide breaks down what carriers are really asking, where most applications fail, and how IT leaders can confidently prove compliance. Download the guide to ensure your next application is backed with verifiable evidence.
Access the eBook
The State of the Cyber Insurance Market
According to industry reporting cited in this guide, 70% of ransomware-related claims were denied in 2025 due to misrepresented or unprovable controls. In many cases, organizations had tools in place, but couldn’t produce the logs, policies, or documentation to prove those controls were enforced at the time of the breach.
If MFA, PAM, or account deprovisioning can’t be demonstrated with evidence, the answer may effectively become “no” when it matters most.

When “Yes” Isn’t Enough
Many organizations check the box for MFA, PAM, or access controls assuming that having the tool in place is enough. It isn’t. Underwriters now expect proof of enforcement, not proof of purchase. That means screenshots of configuration, audit logs tied to real users, documented policies, and evidence that controls were active at the time of a breach.
See How Ready You Really Are
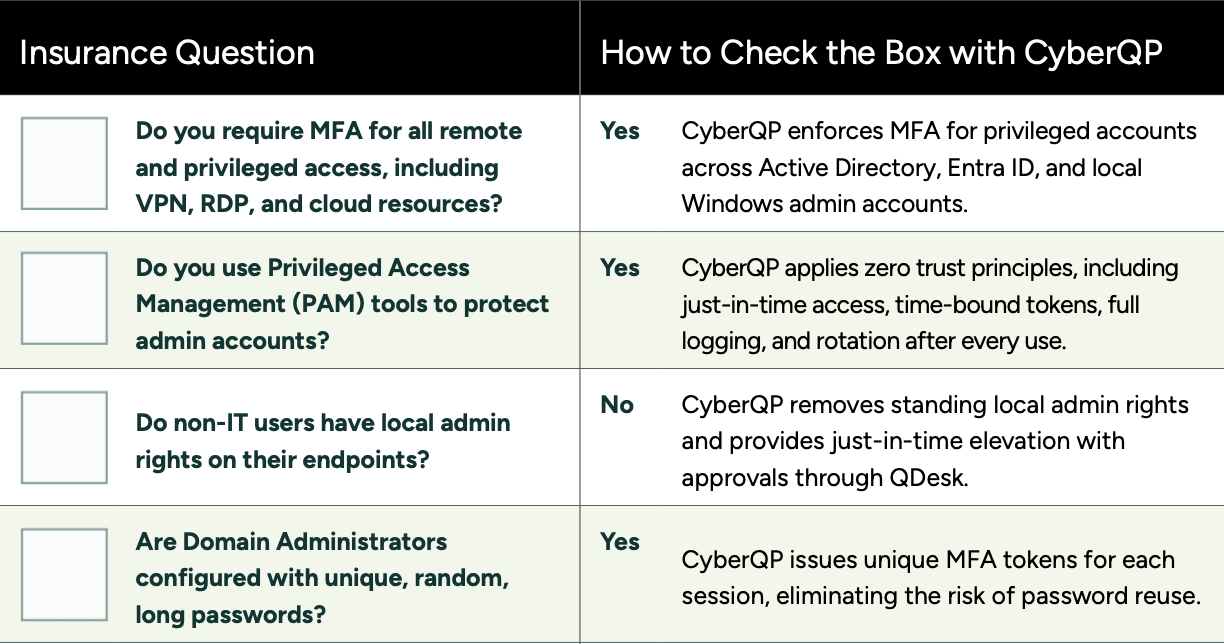
Cyber insurance applications aren’t just about answering “yes.” Underwriters want proof. Our Cyber Insurance Readiness Checklist shows exactly what you’ll be asked and how to demonstrate compliance, from MFA enforcement and privileged access controls to audit-ready evidence and deprovisioning workflows.
With this checklist, you can:
- Quickly verify your security posture before applications hit your inbox
- Ensure every answer is backed by proof, not guesswork
- Protect your coverage and avoid costly denials
Above is a sneak peek of the checklist itself, a practical tool you can print, share with your team, and start using today.