Introducing End-User Elevation: Smarter, Automated Endpoint Privilege Management
We’re excited to unveil End-User Elevation, the next evolution in Endpoint Privilege Management. This powerful update takes security and efficiency to the next level by introducing automated privilege elevation approvals—allowing MSPs and IT Professionals to enforce strict security policies without slowing down end-users or overburdening technicians.
Why does this matter? Managing local admin rights has always been a balancing act between security and productivity. End-User Elevation V1 simplified privilege elevation by providing an easy way for end-users to request access and technicians to approve or deny requests. End-User Elevation eliminates the need for manual approvals for trusted applications, allowing end-users to install and run authorized software without waiting for IT intervention. This streamlines workflows, reduces ticket volume, and fortifies security against unauthorized software installations.
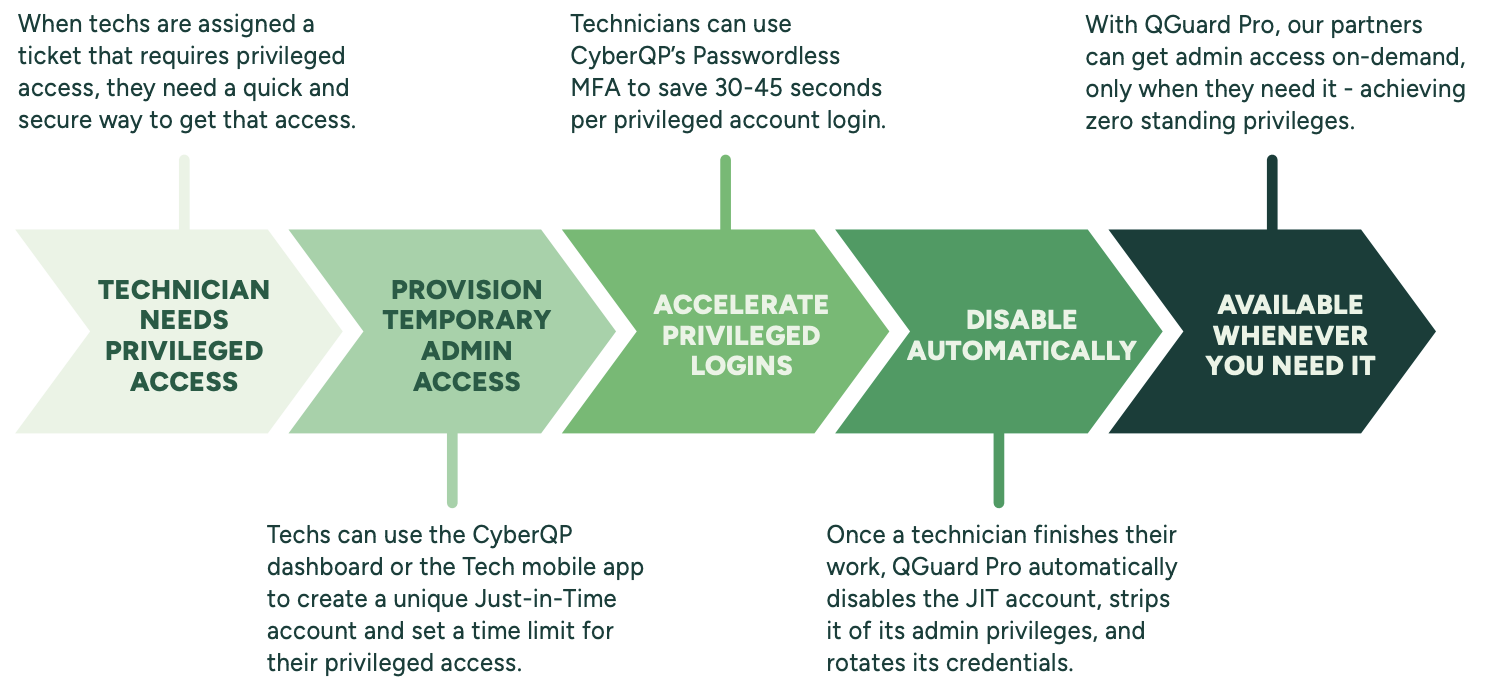
How End-User Elevation Works
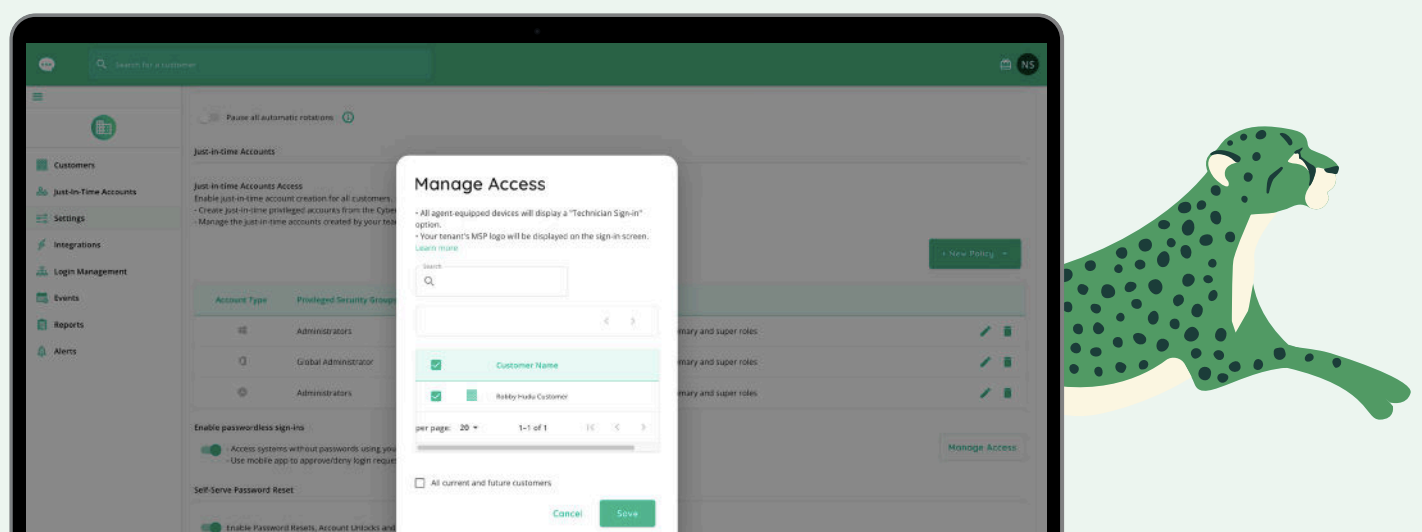
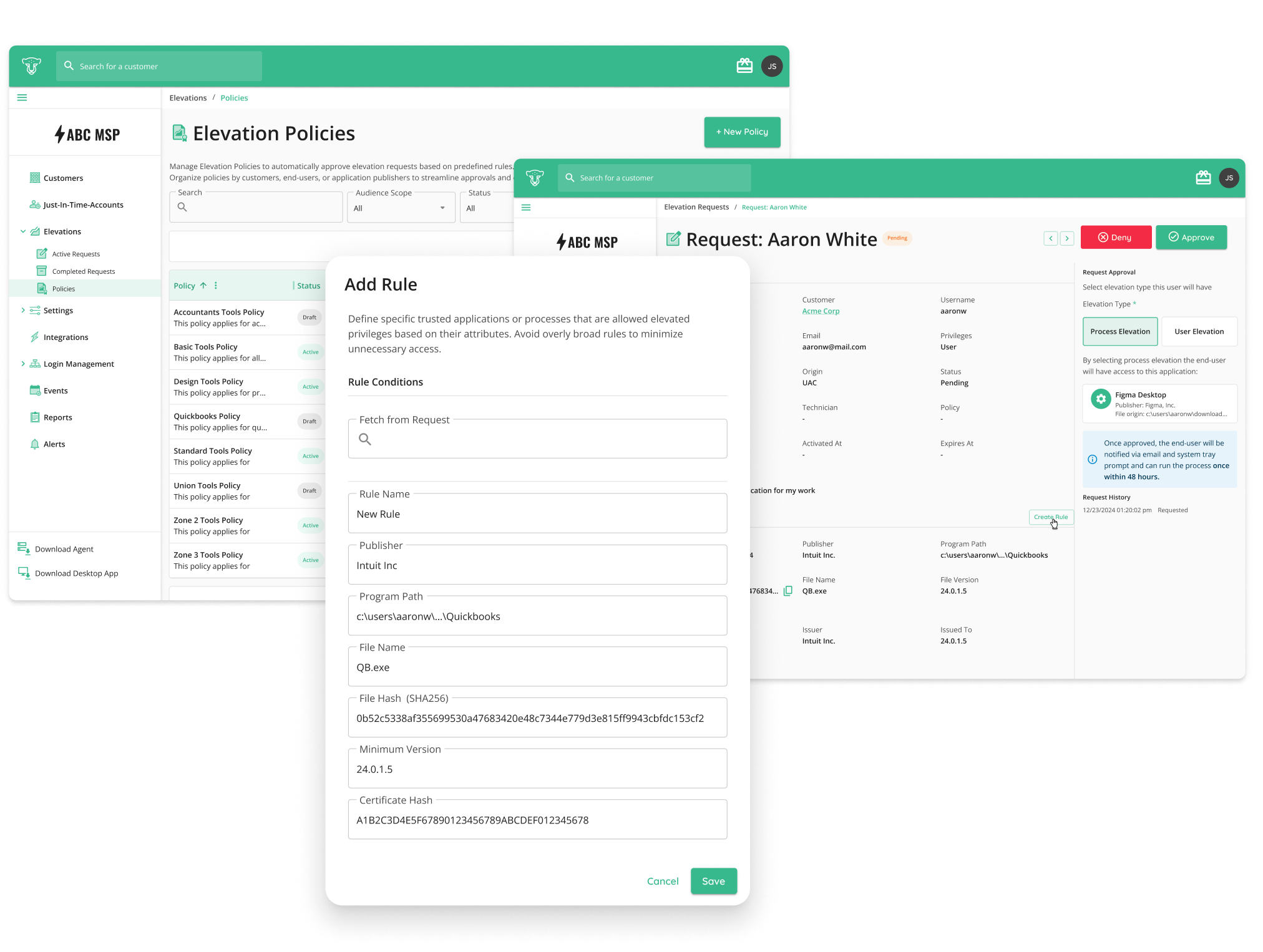
With End-User Elevation, IT Professionals can create smart elevation policies that automatically approve privilege requests based on specific security conditions. These conditions include verifying software publishers, checking file paths, ensuring a secure file hash match, and much more. This ensures only trusted applications are granted elevated privileges—without requiring technician intervention.
For example, you can create a policy that allows accounting team members to install or update QuickBooks (as long as it’s verified as published by Intuit) but blocks unauthorized installers from unknown sources. The result? A seamless end-user experience that enhances security without creating unnecessary IT overhead.
Real-World Benefits for Helpdesks
Stronger Endpoint Security Without Sacrificing Productivity: By implementing automated privilege elevation rules, MSPs and IT Professionals can enforce strict security controls while allowing users to perform essential tasks without disruption. No more back-and-forth approvals for common applications—only verified software gets through.
Fewer Tickets, More Efficiency: Manual approvals take time, and technicians are often bogged down with routine elevation requests. With End-User Elevation handling trusted applications automatically, helpdesks can reduce support tickets and free up technicians to focus on higher-value tasks.
Tailored Access for Every Customer: Every client has different needs. Healthcare organizations might require automatic elevation for EMR software, while legal firms need access to case management tools. End-User Elevation enables custom elevation policies for each customer—ensuring that only the right applications get privileged access.
Granular Control Over Privileged Access: Instead of granting full admin rights, IT can define exactly what applications, processes, and system settings users can access. Policies can be applied at a customer-wide level or for specific users, providing flexibility based on security and compliance requirements.
Logical Privileged Access
When an end-user runs an application requiring elevated privileges, End-User Elevation automatically checks the request against defined policies.
✅ If the request matches an approved policy, the application runs seamlessly.
❌ If the request doesn’t match, the user is prompted to submit a request for technician approval.
For one-off or temporary use cases, technicians retain full control to manually approve privilege elevation requests, ensuring flexibility without compromising security.
What’s Next? Upcoming Enhancements
We’re just getting started! Future updates will bring even more value to End-User Elevation, including:
🔹 PSA Integrations (ConnectWise Manage, Halo, Autotask) – Automatically log elevation requests as tickets in PSA systems for streamlined tracking and auditing.
🔹 Mobile Approvals via QTech App – Technicians will be able to approve or deny elevation requests instantly via push notifications on their mobile devices via QTech app.
🔹 Approval Workflows Inside PSA Tickets – Technicians will be able to manage privilege approvals directly within PSA platforms, reducing context switching and improving efficiency.
End-User Elevation makes privilege management smarter, more secure, and more efficient than ever before. Ready to take it for a spin?
📅 Book a demo to see End-User Elevation in action
🤝 Already a CyberQP partner? Contact your account manager to activate your free trial of End-User Elevation today!